Online ECSAv10 Practice TestMore EC-Council Products >
Free EC-Council ECSAv10 Exam Dumps Questions
EC-Council ECSAv10: EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing
- Get instant access to ECSAv10 practice exam questions
- Get ready to pass the EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing exam right now using our EC-Council ECSAv10 exam package, which includes EC-Council ECSAv10 practice test plus an EC-Council ECSAv10 Exam Simulator.
- The best online ECSAv10 exam study material and preparation tool is here.
Question 1
How many possible sequence number combinations are there in TCP/IP protocol?
Correct Answer:C
Question 2
What will the following URL produce in an unpatched IIS Web Server?
Correct Answer:D
Question 3
Which one of the following 802.11 types has WLAN as a network support?
Correct Answer:C
Question 4
After passing her CEH exam, Carol wants to ensure that her network is completely secure. She implements a DMZ, statefull firewall, NAT, IPSEC, and a packet filtering firewall. Since all security measures were taken, none of the hosts on her network can reach the Internet.
Why is that?
Correct Answer:B
Question 5
The Web parameter tampering attack is based on the manipulation of parameters exchanged between client and server in order to modify application data, such as user credentials and permissions, price and quantity of products, etc.
Usually, this information is stored in cookies, hidden form fields, or URL Query Strings, and is used to increase application functionality and control. This attack takes advantage of the fact that many programmers rely on hidden or fixed fields (such as a hidden tag in a form or a parameter in a URL) as the only security measure for certain operations.
Attackers can easily modify these parameters to bypass the security mechanisms that rely on them.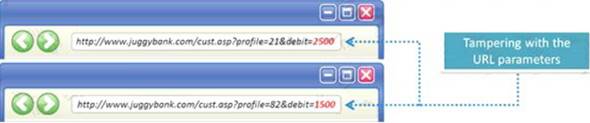
What is the best way to protect web applications from parameter tampering attacks?
Correct Answer:D
Question 6
In a virtual test environment, Michael is testing the strength and security of BGP using multiple routers to mimic the backbone of the Internet. This project will help him write his doctoral thesis on "bringing down the Internet".
Without sniffing the traffic between the routers, Michael sends millions of RESET packets to the routers in an attempt to shut one or all of them down. After a few hours, one of the routers finally shuts itself down.
What will the other routers communicate between themselves?
Correct Answer:C